Moving Beyond the Firewall: A CTO’s Guide to Zero Trust Network Segmentation
Zero trust network segmentation isn’t a feature you bolt onto your security infrastructure; it’s a fundamental architectural decision for modernizing it. It operates on a single, ruthless principle: assume every user, device, and application is hostile until proven otherwise. This model forces every access request to be authenticated and authorized, effectively dismantling the attacker’s primary advantage: lateral movement across a flat network.
Instead of a monolithic perimeter defense, you divide your network into isolated micro-perimeters. For senior technical leaders, the decision is no longer if you should adopt zero trust segmentation, but how to implement it to de-risk modernization initiatives, secure cloud migrations, and build a security posture that can withstand a sophisticated breach.
Why Zero Trust Segmentation Is Non-Negotiable for Modernization
The “castle-and-moat” security model is obsolete. It was designed for a world that no longer exists—one with clear network perimeters. Cloud adoption, distributed architectures, and remote work have dissolved that perimeter, making internal lateral movement the primary vector for catastrophic breaches.
Failing to implement zero trust network segmentation (ZTNS) means your modernized, cloud-native systems remain vulnerable to threats that traditional security was never engineered to stop. It’s a foundational control for protecting your investment in digital transformation.
The Catastrophic Failure of Perimeter-Based Trust
Legacy security architectures operate on a flawed assumption: entities inside the network are trusted. This model fails completely in hybrid and multi-cloud environments where assets are scattered across on-prem data centers and multiple cloud providers.
Once an attacker breaches the perimeter—and they will—they find an open internal network, allowing them to move laterally, escalate privileges, and exfiltrate data. ZTNS counters this by operating under a “breach-assumed” mindset.
By dividing a network into smaller, secure subnetworks, each with its own access controls, segmentation upholds the core Zero Trust principle to “never trust, always verify.” Even if an attacker gains entry, they are effectively trapped within a single segment, unable to access more sensitive systems.
This strategy moves security from a static, location-based control to a dynamic, identity-driven one. Understanding the foundational Zero Trust Security principles is a prerequisite for any successful implementation.
This table breaks down the core philosophical shift between legacy perimeter defense and a modern segmentation strategy.
Core Principles of Zero Trust Segmentation
| Principle | Traditional Perimeter Defense | Zero Trust Network Segmentation |
|---|---|---|
| Trust Model | Trust anything inside the perimeter | Trust nothing; verify every request |
| Access Control | Based on network location (IP address) | Based on identity (user, device, context) |
| Network Visibility | Blind to east-west (internal) traffic | Full visibility into all traffic flows |
| Breach Impact | High; attacker has free lateral movement | Low; breach is contained to one segment |
| Policy Enforcement | Static rules at the edge (firewall) | Dynamic, granular policies per workload |
Implementing a ZTNS model is not a simple technology swap; it’s a complete architectural reimagining of security for a distributed enterprise.
The Undeniable Business Case for Segmentation
The market’s massive investment underscores its criticality. The global Zero Trust Network Access (ZTNA) market, where segmentation is a core component, is projected to explode from USD 3.91 billion in 2025 to USD 26.50 billion by 2034, a CAGR of 23.7%. The market data for Zero Trust Network Access adoption clearly shows this is not speculative hype.
The ROI is concrete. Organizations with mature segmentation detect threats 59% faster, directly translating into millions of dollars in averted losses from data breaches and operational downtime.
For a CTO or VP of Engineering steering modernization, segmentation is a core enabler for business agility and resilience. It is what lets you:
- Secure Cloud Migration: Isolate legacy workloads as you move them to the cloud, protecting them and the new environment from cross-contamination.
- Protect Critical Applications: Create secure enclaves around high-value assets and sensitive data, irrespective of their physical or virtual location.
- Enable Secure DevOps: Enforce strict, automated controls between development, testing, and production environments, securing the CI/CD pipeline from supply chain attacks.
Without zero trust network segmentation, your modernization efforts build new features on a foundation of archaic, ineffective security.
Architecting Your Segmentation Blueprint: Macro vs. Micro
The primary architectural decision in a ZTNS project is choosing between macro-segmentation and micro-segmentation. This choice dictates your implementation path, tooling, and timeline. It is not a one-size-fits-all decision; it depends on your existing architecture, risk tolerance, and the pace of your modernization efforts.
Legacy security models are broken. Modern threats don’t stop at the firewall; they exploit internal vulnerabilities to spread laterally. Segmentation is your most effective defense against this attack pattern.
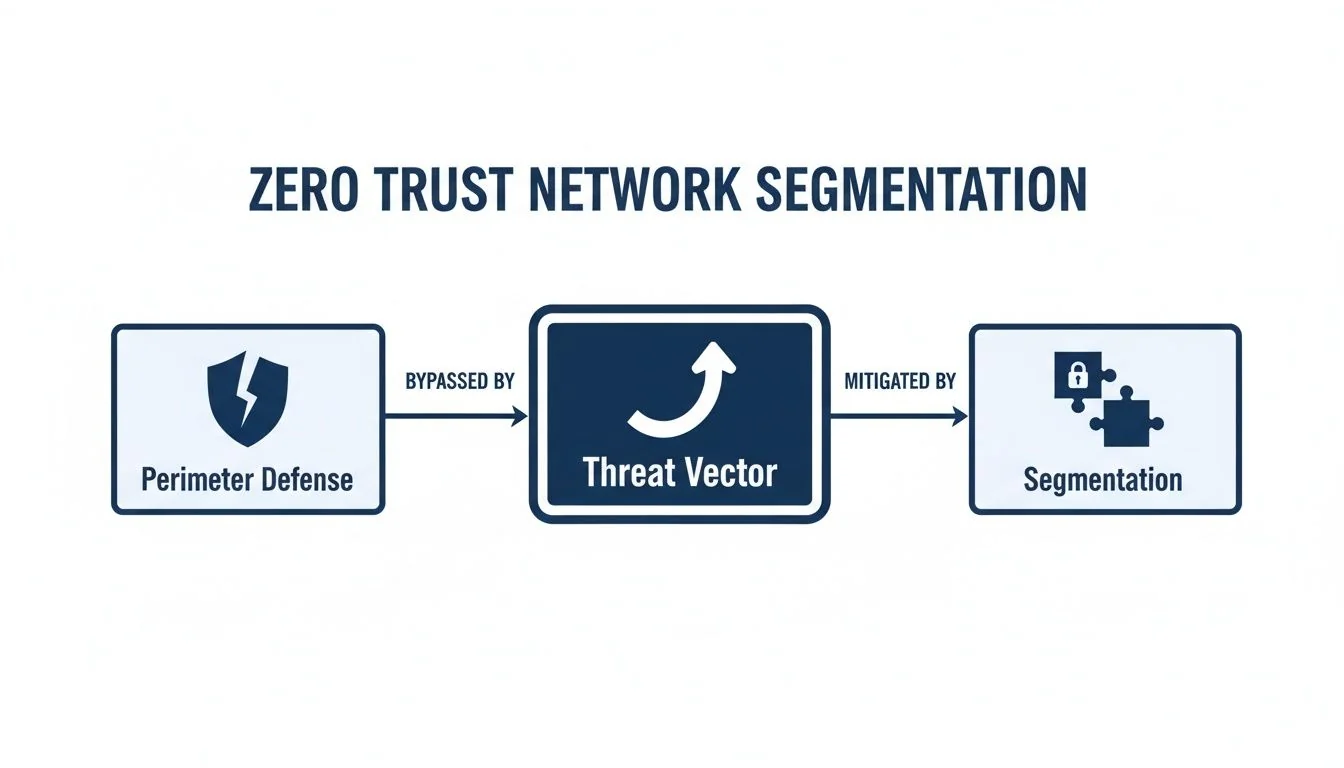
As the diagram shows, once an attacker gains initial access, segmentation is the only control that prevents a minor breach from escalating into a full-blown crisis.
Macro-Segmentation: A Pragmatic First Step
Macro-segmentation involves creating broad, logical boundaries across your network. This means creating separate zones for production workloads, development environments, and corporate IT. It’s a practical approach that delivers immediate risk reduction without the complexity of a complete network overhaul.
This is typically implemented with existing tools like Next-Generation Firewalls (NGFWs) and Virtual LANs (VLANs). It is effective for preventing coarse-grained violations, such as a developer’s workstation directly accessing a production database. However, it provides no protection against an attacker who has already compromised a server within a production segment. A concerning 75% of organizations still rely on this brittle and difficult-to-manage method, leaving them exposed to internal threats.
Micro-Segmentation: The Granular End Goal
Micro-segmentation is the definitive implementation of a zero trust strategy. Instead of large network zones, you create a secure perimeter around every individual workload—each VM, container, or serverless function. The attack surface shrinks dramatically, making lateral movement nearly impossible.
Micro-segmentation is the principle of least privilege enforced at the network level. If a web server is compromised, it cannot communicate with the adjacent database unless an explicit policy allows it. The breach is contained instantly.
Achieving this level of granularity requires a modern, software-defined toolkit:
- Software-Defined Perimeters (SDP): Create one-to-one encrypted tunnels between a user and a resource, rendering the underlying infrastructure invisible to unauthorized entities.
- Agent-Based Solutions: Install lightweight agents on each host (server, VM) to enforce security policies directly at the workload, independent of the network topology.
- Native Cloud Controls: Leverage built-in cloud platform tools like AWS Security Groups or Azure Network Security Groups, which act as stateful firewalls for every cloud instance.
Micro-segmentation is the destination, not the starting point. It demands deep application visibility and a mature policy-as-code practice. A comprehensive zero trust architecture design is required to integrate these components effectively.
Decision Framework: A Phased Approach
This is not a binary choice. Successful ZTNS projects adopt a phased journey.
- Start with Macro-segmentation: Implement broad controls to secure quick wins and wall off critical environments. This stops the most obvious bleeding.
- Apply Micro-segmentation Surgically: Target high-value assets first—new cloud-native applications, critical databases, and systems holding sensitive data.
- Expand Incrementally: Over time, expand granular controls across the rest of the enterprise as part of your ongoing modernization roadmap.
This hybrid approach balances the ideal security state with operational reality, preventing the “boil the ocean” syndrome that dooms most large-scale security projects.
Implementation Patterns and Common Failure Modes
A ZTNS strategy is worthless without flawless execution. The objective is not to create a web of policies that grinds business operations to a halt, but to implement surgical controls that protect high-value assets without introducing friction.
Success depends on a clear view of what you are protecting. We have found that two high-impact patterns consistently deliver the greatest risk reduction and build momentum for broader adoption.
Pattern 1: Protecting High-Value Applications
Your “crown jewel” applications—those processing sensitive PII, financial transactions, or intellectual property—are the obvious first target. The strategy is to create a secure enclave using micro-segmentation, isolating them from the general network.
This is a tactical, three-step process:
- Map All Dependencies: Use a traffic visibility tool to create a definitive map of every inbound and outbound connection for the application. You cannot protect what you cannot see. This step is non-negotiable.
- Define and Test Policies: Draft allow-list policies based on the legitimate traffic flows identified. Run these policies in a “monitor-only” or “logging” mode for several weeks to identify exceptions and legitimate edge cases without causing an outage.
- Enforce and Lock Down: Once you are confident the policies accurately reflect required communications, switch to enforcement mode. All unauthorized traffic is now blocked by default.
The payoff is immediate. Even if an adjacent, less-secure system is compromised, the attacker has no network path to the critical application.
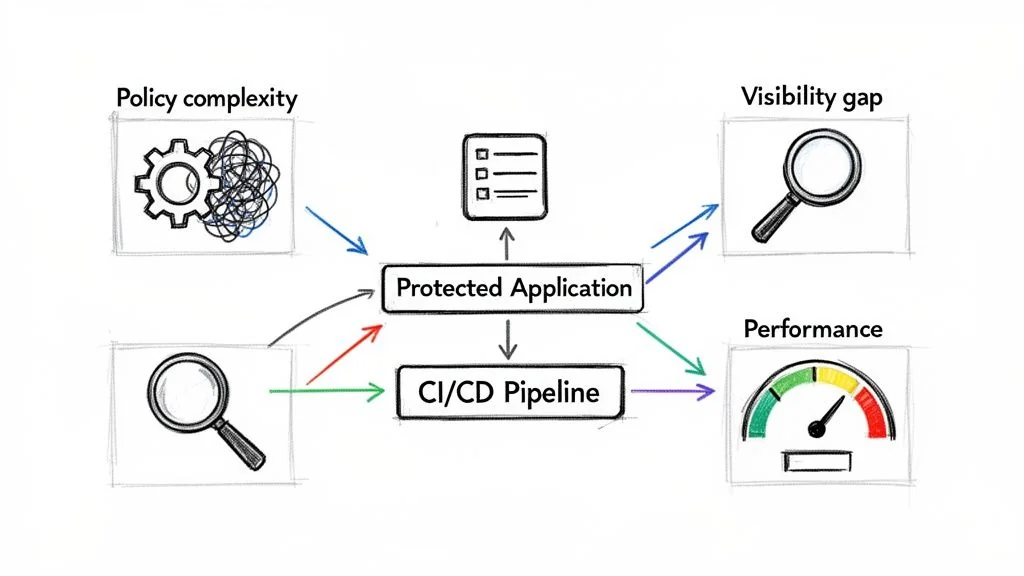
Pattern 2: Securing the CI/CD Pipeline
A modern software delivery pipeline is a prime target for supply chain attacks. A compromised build server or artifact repository allows an attacker to inject malicious code into every application you ship. Securing this pipeline with zero trust network segmentation is not optional.
This requires isolating each stage of the pipeline at the network level:
- Development: Developer environments must have zero direct network access to production infrastructure.
- Build: The build server must only be allowed to pull code from a trusted source repository and push to a specific artifact repository. All other communication is blocked.
- Testing: Staging and testing environments must be completely isolated from production. There is no acceptable reason for test systems to have a network path to live data.
- Production: Only the automated deployment tool (e.g., Argo CD, Spinnaker) should have the credentials and network access required to push new artifacts into the production environment.
This enforces separation of duties at the network level, creating a secure software factory that is resilient to tampering.
Common Failure Modes and How to Avoid Them
ZTNS projects fail due to operational missteps, not technology limitations. Just 5% of organizations are micro-segmenting their networks today because these challenges feel insurmountable. If you want to implement Zero Trust security successfully, you must anticipate these failure modes.
- Overly Complex Policies: Teams attempt to write hyper-granular rules for every workload from day one, creating an unmanageable mess that leads to outages. Avoid this by starting with broader, environment-level policies and refining them iteratively.
- Poor Application Visibility: Deploying policies without a complete dependency map is a recipe for failure. You will either break applications or leave gaping security holes. Avoid this by investing in visibility and traffic mapping tools before writing a single enforcement rule.
- Performance Bottlenecks: Some segmentation solutions, particularly those that proxy all traffic through a central appliance, introduce unacceptable latency. Avoid this by choosing solutions that enforce policy at the host level where possible and by rigorously performance testing them against production-level traffic loads.
For VPs of Engineering driving modernization, the data is stark: without proper segmentation, a 59% faster threat detection capability evaporates. This only magnifies the 67% project failure risk already present in complex cloud migrations. While vendors like Zscaler and Fortinet offer powerful Software-Defined Perimeter (SDP) solutions, be warned—over-customization is a budget killer. A staggering 30% of large-scale rollouts exceed budgets by 50% because of underestimated legacy integration costs.
Choosing Your ZTNS Vendor: A Defensible Decision Matrix
Choosing the right technology and implementation partner is the single highest-leverage decision you will make in a ZTNS project. A mismatch between your architecture and a vendor’s core technology is the number one driver of failure. You cannot rely on marketing slicks; you need a structured, evidence-based framework to make a defensible choice.
The goal is not to find the “best” vendor, but the right vendor for your specific environment, your team’s capabilities, and your modernization roadmap. A solution built for cloud-native startups will fail in a legacy-heavy enterprise.
The Only Evaluation Criteria That Matter
Your evaluation must focus on three core areas: technical alignment, integration depth, and total cost of ownership (TCO). These factors determine whether a solution will actually work in your real-world environment.
- Technical Specialization: Does the vendor specialize in agent-based or agentless deployments? Is their “cloud-native” solution a repackaged on-prem product? A vendor excelling at agentless, on-prem segmentation is the wrong choice for securing ephemeral workloads in Kubernetes.
- Integration Ecosystem: A ZTNS tool cannot operate in a silo. It must have deep, native integrations with your Identity Provider (Okta, Azure AD), SIEM, and CI/CD pipeline. A weak IdP connection renders identity-based policies useless.
- Total Cost of Ownership (TCO): Look beyond the license price. Factor in the hidden costs of implementation, ongoing operational overhead, and performance impact. Agent-based tools may demand more management cycles, while network-based approaches can force expensive hardware upgrades.
Effective segmentation is non-negotiable for any CTO trying to de-risk a legacy system modernization, which can otherwise have failure rates as high as 67%. When you overlay zero trust controls, modernization costs can range from $2.50 to $5.00 per line of code. The payoff is significant: segmented organizations report up to 70% better compliance outcomes—a critical defense against fines like the $14.8 million average for GDPR violations. Market research on zero trust security trends confirms these impacts.
A Framework for a Bulletproof Decision
Use a quantitative scoring matrix to move the decision from gut-feel to a data-driven conclusion. Assign a weight to each criterion based on what is mission-critical for your organization, not what the vendor’s sales team emphasizes.
A classic mistake is over-weighting “advanced features” you will never use while underweighting “ease of policy management.” A sophisticated tool that no one can operate is more dangerous than a simpler tool that is configured correctly 100% of the time.
This matrix forces an explicit discussion about priorities and provides a defensible rationale for your final choice.
Vendor and Partner Evaluation Matrix
Adapt this scoring matrix to drive your evaluation. Be brutally honest in your scoring and in the “Notes & Red Flags” column—that is where the decision is truly made.
| Evaluation Criteria | Weight (1-5) | Vendor A Score (1-10) | Vendor B Score (1-10) | Notes & Red Flags |
|---|---|---|---|---|
| Agent vs. Agentless Alignment | 5 | 8 | 4 | Vendor B is primarily agent-based; our environment is 70% unmanaged legacy. Dealbreaker. |
| IAM/IdP Integration Depth | 5 | 9 | 7 | Vendor A has native connectors for our IdP. Vendor B requires a custom script. High risk. |
| SIEM & SOAR Integration | 4 | 7 | 8 | Both are solid. Vendor B provides richer, more actionable log formats for our SOAR playbooks. |
| Multi-Cloud Policy Consistency | 4 | 6 | 9 | Vendor B’s policy engine is way better at abstracting cloud-native controls. Huge plus. |
| Performance Impact (Latency) | 3 | 8 | 5 | Lab tests show Vendor B adds 15ms of latency to database queries. Red flag. |
| Policy Management Overhead | 5 | 7 | 4 | Vendor B’s model would require three full-time engineers for policy upkeep. Not happening. |
| TCO (3-Year Projection) | 4 | 9 | 6 | Vendor A is 20% cheaper over three years once we factor in operational and staffing costs. |
| Partner Expertise with Legacy | 5 | 8 | 3 | Vendor A’s partner has a proven, verifiable track record with mainframe modernization. |
This structured analysis removes emotion and ensures the zero trust network segmentation solution you choose aligns with your architecture, team, and modernization goals.
Phased Migration From Legacy to Segmented
A “big bang” migration to zero trust network segmentation is a recipe for career-limiting outages. Attempting to segment an entire flat, legacy network overnight will break critical applications, burn out your engineering teams, and get the project canceled. The only viable strategy is a phased, pragmatic approach.
This “crawl-walk-run” model systematically de-risks the transition by delivering small, incremental wins, building momentum, and avoiding the catastrophic business disruption that sinks overly ambitious rollouts.
The Crawl Phase: Discovery and Visibility
You cannot segment what you cannot see. This initial phase is solely about discovery and mapping, with zero enforcement. Rushing this step is the single most common reason segmentation projects fail. With 64% of organizations connecting over 5,000 assets to their networks, manual discovery is impossible. You will miss critical dependencies.
Your only goal here is to build a high-fidelity map of all network assets and their communication patterns. This is also the time to gain buy-in from application owners by framing the project around reducing risk to their services, not as a top-down security mandate.
The goal of the Crawl phase isn’t to block a single packet. It’s to build a map of reality. Any policy written without this foundation is pure guesswork and will inevitably break production.
With this map, you can draft policies in a “monitor-only” mode, allowing you to test your assumptions against live traffic and identify missed dependencies without causing downtime.
The Walk Phase: Your First Kill
With a validated traffic map and stakeholder buy-in, you can move to limited enforcement. Start small by securing a quick win. A new cloud-native application or a well-understood, isolated legacy service is an ideal candidate.
Here, you apply your first real micro-segmentation policies, creating a secure enclave around the pilot application. The rules refined during the monitoring period are now switched to “enforce.” This delivers a fast, tangible victory you can use to prove the value of ZTNS to leadership.
Your checklist for this phase is simple:
- Select a Pilot App: Choose a non-critical but visible application where the owners are cooperative.
- Enforce Policies: Switch the validated rules from “monitor” to “block” for the pilot segment.
- Establish a Baseline: Measure performance and document all operational issues to create a feedback loop.
- Communicate the Win: Demonstrate the real risk reduction by showing how the pilot app is now isolated from lateral threats.
The Run Phase: Scaling Across the Enterprise
With successful pilots complete, the Run phase is about systematically expanding segmentation across the enterprise. You use the lessons, refined policies, and operational playbooks from your initial wins to accelerate deployment into more complex and critical environments.
This is where you can tackle harder challenges, such as isolating a monolith as part of a larger legacy system modernization initiative to contain its risk before a full refactor.
Policy automation becomes critical at this stage. As you scale from a few segments to hundreds, manual rule management becomes impossible. You must adopt a policy-as-code model, integrating your segmentation platform with your CI/CD pipeline to automate rule creation, testing, and deployment. At this point, segmentation is no longer a project; it is simply how you operate.
Measuring Success: KPIs and Runbooks for Your ZTNS
A zero trust network segmentation strategy is only as good as its operational reality. To justify the investment and prove its value, you must move from a project mindset to a continuous cycle of measurement and response. Without hard metrics and pre-scripted runbooks, your architecture is just a complex firewall with no provable impact on risk.
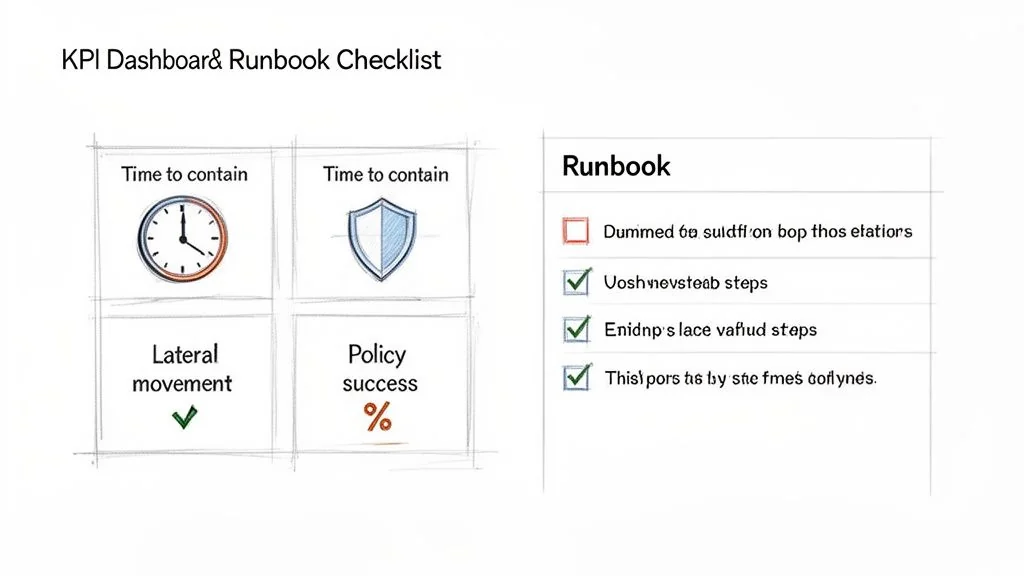
Focus on KPIs that directly map to security posture and resilience, not vanity metrics.
Defining the KPIs That Actually Matter
Your KPIs must be tied to concrete security outcomes that demonstrate a quantifiable reduction in business risk. Focus on these core indicators:
- Reduction in Detected Lateral Movement: This is the ultimate test. Track alerts from your SIEM or EDR flagging east-west threat activity. In a successful ZTNS implementation, this number should plummet, proving that even when a host is compromised, the attacker is contained.
- Time to Contain (TTC): Measure the time from the initial alert of a compromised asset to the moment you confirm its full isolation. With proper segmentation and automated runbooks, TTC should drop from hours or days to minutes. A 90% reduction is a realistic target for a mature program.
- Policy Enforcement Success Rate: Track the ratio of blocked, illegitimate connection attempts to allowed, legitimate ones. A high success rate (e.g., 99.9%) proves your policies are effective at stopping threats without causing business disruption from false positives.
The most critical failure of a ZTNS rollout is treating it as a one-time project. Continuous monitoring of these KPIs is the only way to ensure your policies adapt as your environment changes and your security investment continues to deliver value.
Building Your Operational Runbooks
When a security event occurs, the response must be fast, precise, and pre-scripted. Operational runbooks turn incident response from a chaotic scramble into a predictable, repeatable process.
Your ZTNS runbooks must address specific scenarios with clear, step-by-step actions.
Scenario: Unauthorized Access Attempt Detected
- Automated Trigger: The SIEM detects a blocked connection attempt to a critical database from an unauthorized workload and fires an alert.
- Instant Isolation (Automated): A SOAR playbook is triggered, placing the source workload into a “quarantine” segment with zero outbound network access, instantly containing the threat.
- Alert & Ticket: The on-call engineer receives a PagerDuty alert, and a Jira ticket is automatically created with all relevant logs, asset tags, and policy context.
- Forensic Analysis: The engineer analyzes the quarantined workload in a sandboxed environment, completely isolated from production.
- Remediation & Recovery: Based on the analysis, the workload is either terminated or cleaned and returned to its proper production segment.
This structured response ensures containment is immediate and investigation is efficient, turning a good architecture into a resilient security operation.
Answering the Tough ZTNS Questions (That Vendors Dodge)
Even with a perfect blueprint, the real-world implementation of zero trust network segmentation runs into hard questions that vendor marketing materials conveniently ignore. Here are the straight answers for CTOs and architects in the trenches.
How Does Micro-segmentation Impact Network Performance?
It depends entirely on the architecture. Agent-based solutions are the clear winner, enforcing policy on the host with negligible latency. In contrast, older network-based or firewall-centric models that force traffic through a central chokepoint can severely degrade performance.
For any high-throughput or latency-sensitive application, host-based micro-segmentation is the only viable path. A performance penalty of even 5-10ms per transaction can cripple a real-time system. Rigorously test any solution against your actual production traffic loads before making a commitment.
Can ZTNS Be Applied to OT and IoT Environments?
Yes, but not with your standard IT toolset. Operational Technology (OT) and IoT devices often run on legacy or minimal operating systems that cannot support a security agent and use specialized industrial protocols.
For these environments, the only effective strategy is agentless zero trust network segmentation. This is enforced by network hardware like Next-Generation Firewalls (NGFWs) or specialized OT security appliances. The approach is to create isolated zones around groups of similar devices (e.g., HVAC controllers, manufacturing PLCs) and lock down communication to known-good patterns.
How Do You Manage Policies at Scale?
Manual management of thousands of granular rules is a guaranteed failure that leads to misconfigurations and security gaps.
The only scalable solution is policy-as-code. Segmentation rules must be defined in a declarative format (e.g., YAML), stored in a Git repository, and deployed through an automated CI/CD pipeline. This provides version control, peer review, and automated testing. Large enterprises, which will account for 59.62% of all ZTNS spending by 2026, are already standardizing on this model to manage risk. Analysis of zero trust network architecture trends confirms that this level of automation is rapidly becoming the industry standard.
How Do You Gain Visibility Into Encrypted Traffic?
You do not need to break TLS/SSL everywhere. Widespread “man-in-the-middle” decryption is resource-intensive and creates significant privacy and compliance risks.
A more pragmatic approach is to focus on metadata. Modern ZTNS solutions can infer traffic context and enforce policy based on metadata alone—such as source, destination, and identity—without decrypting the payload. This provides robust security without crippling performance or creating a compliance disaster.