A CTO's Guide to Defusing Legacy Authentication System Risks
Legacy authentication systems are not technical debt. They are an active, ticking financial time bomb on your balance sheet. Outdated protocols like Basic Auth are fundamentally incompatible with modern, zero-trust security models. They create unguarded backdoors that completely bypass MFA and other controls, leading directly to high-impact identity breaches.
These are not abstract threats. They are active, quantifiable risks that will hit your bottom line.
The Escalating Cost of Inaction
The conversation around legacy auth has moved past “what if” to “when and how much.” The numbers are concrete. 87% of breaches are now tied to identity vulnerabilities, costing an average of $2.5 million per incident.
The 2025 HYPR State of Passwordless Identity Assurance report confirms that nearly half of all firms were breached last year. These incidents are fueled by a relentless barrage of password attacks—happening at a rate of 7,000 per second—and supercharged by GenAI tools that make credential stuffing and phishing brutally effective. You can review the in-depth analysis on why 2025 is a critical year for killing legacy authentication.
Direct and Indirect Financial Bleeding
The financial drain is not a one-time hit from a breach. It is a continuous bleed on resources that many executives miss until it is too late. The costs compound across key areas that must be on every CTO’s radar:
- Soaring Operational Overhead: Your best engineers and IT teams are wasting time managing password resets, troubleshooting locked accounts, and applying emergency patches to brittle, unsupported systems. This is expensive, low-value work that derails innovation.
- Skyrocketing Cyber Insurance Premiums: Underwriters now scrutinize authentication methods. The presence of protocols like SMTP AUTH with Basic Auth is a massive red flag that directly translates to higher premiums or outright denial of coverage.
- Blocked Digital Transformation: Legacy dependencies act like a sea anchor, dragging down or stalling critical cloud migrations and app modernization projects. Every custom integration and workaround adds cost and complexity, inflating project budgets and cratering timelines.
The real financial risk of legacy authentication is the opportunity cost. While your teams patch 20-year-old protocols, your competitors deploy modern identity solutions that accelerate their business and build a security posture that withstands modern attacks.
The table below breaks down the tangible impacts. This is a summary of what we see in the field with clients before they modernize.
Legacy Authentication Risk Impact Matrix
| Risk Category | Description | Quantifiable Business Impact | Affected Area |
|---|---|---|---|
| Security | Protocols like Basic Auth cannot enforce MFA, making them prime targets for password spray and credential stuffing attacks. | Average breach cost: $2.5M. Increased cyber insurance premiums by 20-50% or denial of coverage. | Security, Finance, Legal |
| Availability | Outdated systems are prone to failure and are being actively deprecated by major vendors, leading to service outages. | Application downtime costs, emergency migration expenses (2-3x planned costs), loss of customer trust. | Operations, Engineering, Sales |
| Compliance | Failure to meet modern identity standards violates regulatory requirements like GDPR, CCPA, and industry-specific mandates. | Regulatory fines (up to 4% of global revenue), audit failures, and reputational damage. | Compliance, Legal, Marketing |
| Operational | High volume of password resets and account lockouts drain IT and helpdesk resources on low-value, repetitive tasks. | Increased support tickets by 30-40%. Wasted engineering hours on patching instead of innovation. | IT, Engineering, HR |
This matrix is not a list of problems; it is a financial forecast. Each of these risks represents a future line item on an incident response invoice or a budget overrun report.
The Inescapable Deprecation Horizon
This is no longer a choice. Protocols like Basic Auth are being aggressively deprecated by the providers you rely on. Microsoft Exchange Online will permanently disable Basic Auth for SMTP AUTH by April 30th, 2026. This is not a suggestion; it is a hard deadline.
Companies that fail to modernize will face a sudden cliff of service disruptions, broken applications, and a last-minute scramble that is exponentially more expensive than a planned migration. The choice is no longer if you will move off legacy auth, but whether you do it on your own terms or on a vendor’s forced, chaotic timeline.
The cost of a single identity-driven breach now dwarfs the investment in a modern security architecture. This is a strategic imperative for business survival.
How to Categorize Your Legacy Authentication Risks

Lumping all legacy authentication issues into one “technical debt” bucket guarantees inaction. It makes the problem feel insurmountable, paralyzing any real progress. A vague “legacy” label is useless when you are trying to get budget or explain the business impact to your board.
To make headway, you must break the problem down into specific risk domains. This is how you move from overwhelmed inaction to a targeted plan. It allows you to prioritize fixes based on what will hurt the business most.
Security Risks
This is the most obvious and urgent category. We are talking about protocols that are fundamentally broken by modern standards. They do not support MFA, they broadcast credentials with little to no protection, and they create backdoors that bypass all your expensive, modern security controls.
- Credential Theft: Protocols like POP3, IMAP, and SMTP using Basic Auth are notorious for this. They send usernames and passwords in a way that makes them trivial to intercept.
- Brute-Force & Password Spraying: These legacy endpoints are the front door for automated attacks. Since they cannot enforce MFA or smart lockout policies, attackers can hammer them with millions of password combinations until they get a hit. The BAV2ROPC pattern, for instance, is a well-known favorite for hammering Microsoft Entra ID.
- MFA Bypass: This is the killer. The existence of a single application using a legacy protocol completely undermines your entire MFA strategy. An attacker who finds that one weak link can walk right past all your other defenses with a stolen password.
Operational Risks
These are the silent killers that drain your team’s efficiency, tank system stability, and bloat your budget. Their cumulative effect is a constant tax on your resources.
Legacy authentication is not just a security problem; it is an operational bottleneck. Every hour your engineering team spends troubleshooting a brittle, unsupported authentication system is an hour they are not spending on innovation that drives revenue. This silent tax on productivity is a major hidden cost.
This operational drag shows up in a few key ways:
- Excessive Support Tickets: A huge chunk of helpdesk tickets—often 30-40%—are for password resets and account lockouts. This problem is baked into the design of password-dependent legacy systems.
- Forced Deprecation & Outages: Vendors are done supporting these old protocols. Microsoft’s hard deadline for shutting down Basic Auth for SMTP AUTH is a perfect example. If you ignore these deadlines, you are choosing to have your applications suddenly break.
- Inhibited Scalability: These old systems were not built for the cloud. They are often stateful, a nightmare to containerize, and cannot scale horizontally. As your user base grows, they become performance bottlenecks.
Compliance and Governance Risks
Regulators and auditors are no longer giving a pass on identity security. Sticking with outdated authentication methods creates glaring compliance gaps that lead to eye-watering fines and serious reputational damage. A proper cybersecurity risk assessment is the first step to formally identifying and documenting these gaps before an auditor does it for you.
Key compliance risks include:
- Audit Failures: Cannot enforce MFA? Cannot produce a clean audit trail for user access? You are setting yourself up to fail audits for crucial frameworks like SOC 2, HIPAA, and PCI DSS.
- Regulatory Fines: Data protection laws like GDPR and CCPA have teeth. If a breach is traced back to weak authentication, the fines can be catastrophic, reaching up to 4% of global annual revenue.
- Loss of Certifications: Your ability to operate in certain industries often hinges on certifications that mandate modern identity and access management. Clinging to legacy tech puts those certifications—and that revenue—at risk.
Migration-Specific Risks
This last category is critical for any CTO or VP of Engineering planning a move to the cloud. Dependencies on legacy authentication are one of the top reasons modernization projects go off the rails. For a deeper look, see our guide on conducting a legacy assessment before you migrate.
- Intertwined Dependencies: Finding out your monolithic application has hardcoded Kerberos dependencies is a classic migration nightmare. Untangling that mess requires specialized, expensive expertise and can derail your project timeline.
- Service Account Hell: This is a huge, often undocumented problem. Countless scripts, automated processes, and service accounts are running with static credentials buried in config files. This creates a massive attack surface that is difficult to migrate securely without breaking critical business processes.
Real-World Attack Vectors That Exploit Legacy Systems
Theoretical risks are easy to dismiss. A breach notification makes them real. Attackers are not using zero-day exploits; they are walking through the front door using a documented playbook that targets your legacy authentication protocols.
These methods work because protocols like Basic Auth were designed for a time when “inside the network” meant “trusted.” In today’s zero-trust reality, that makes them a backdoor. Attackers know that if they can find a single endpoint speaking a legacy protocol, they have found a way to bypass your MFA and Conditional Access policies.
MFA Fatigue and Protocol Downgrade Attacks
One of the most common entry points is a protocol downgrade attack. An attacker gets a compromised credential—often from phishing—and then intentionally targets your oldest endpoints, like IMAP, POP3, or ancient Exchange ActiveSync connections.
These protocols do not know how to handle a modern authentication challenge, so they fall back to a simple username and password check. This creates a massive blind spot. While your modern apps are secured with phishing-resistant MFA, the attacker sidesteps those controls by finding an old service that still accepts Basic Auth. They are in, and your primary defense never fired.
A related—and brutally effective—technique is MFA fatigue bombing. Armed with a valid credential, attackers hammer a user’s account with login attempts, flooding their device with push notifications. The goal is to annoy or confuse the user into tapping “Approve.” Legacy systems lack the sophisticated throttling and risk-detection needed to shut down these high-velocity attacks.
Abusing OAuth Legacy Flows and BAV2ROPC
Even modern-seeming hybrid environments are not safe. Attackers actively exploit legacy OAuth flows and specific endpoints like BAV2ROPC (a legacy endpoint in Microsoft environments) to run credential-stuffing and password-spray campaigns. These older flows lack the robust security checks of modern OAuth 2.0.
Between March 18 and April 7, 2025, security researchers documented a targeted campaign that exploited legacy authentication in Microsoft Entra ID. This campaign triggered over 9,000 suspicious Exchange login attempts, including 12,221 via OAuth Legacy Flow and a staggering 27,332 via Basic Auth. The numbers show how relentlessly attackers hammer these weak points.
The existence of legacy protocols creates a permanent “attack surface of last resort.” When modern defenses block an attacker’s primary approach, they do not give up. They methodically scan for and pivot to the weakest, oldest authentication method you have left enabled.
Unmanaged Secrets and Service Account Compromise
The other ticking time bomb is the mess of service accounts and embedded secrets. Legacy applications and ancient deployment scripts are infamous for having credentials—passwords, API keys, tokens—hardcoded directly into config files or source code. For an attacker, these static secrets are gold.
Once an intruder gains a foothold, their first move is to scan repositories and file systems for these exposed credentials. A startling number of real-world breaches hinge on improperly managed secrets. It is why a robust strategy, including tools for GitHub Secret Scanning, is no longer optional.
- Service Account Hijacking: A compromised service account is often the jackpot. These accounts usually have broad, elevated permissions, giving an attacker the keys to the kingdom. They can move laterally, access critical databases, and exfiltrate data for months without detection.
- SIM Swapping for Account Recovery: This vector bypasses passwords entirely. An attacker convinces a mobile carrier to transfer a key employee’s phone number to a SIM card they control. They then hit “forgot password” on a critical account, intercept the SMS-based recovery code, and take over. It is a direct exploit of a weak, legacy form of identity verification.
These attack vectors tell a single, critical story: legacy authentication is not just weak; it is fundamentally incompatible with modern security. It provides a reliable path for attackers to walk right past your most important defenses.
A Phased Modernization Playbook That Actually Works
A “rip and replace” approach to legacy authentication is a career-limiting move. It is a fantasy that ignores decades of brittle, undocumented dependencies. The only defensible strategy is a phased, pragmatic migration that methodically untangles this mess without causing a catastrophic outage.
The goal is a controlled process that builds a bridge to a modern identity fabric while the old system still runs. This playbook is the step-by-step framework to get it done.
First, understand exactly what you are up against. Attackers love legacy protocols because they provide a backdoor around modern security controls.
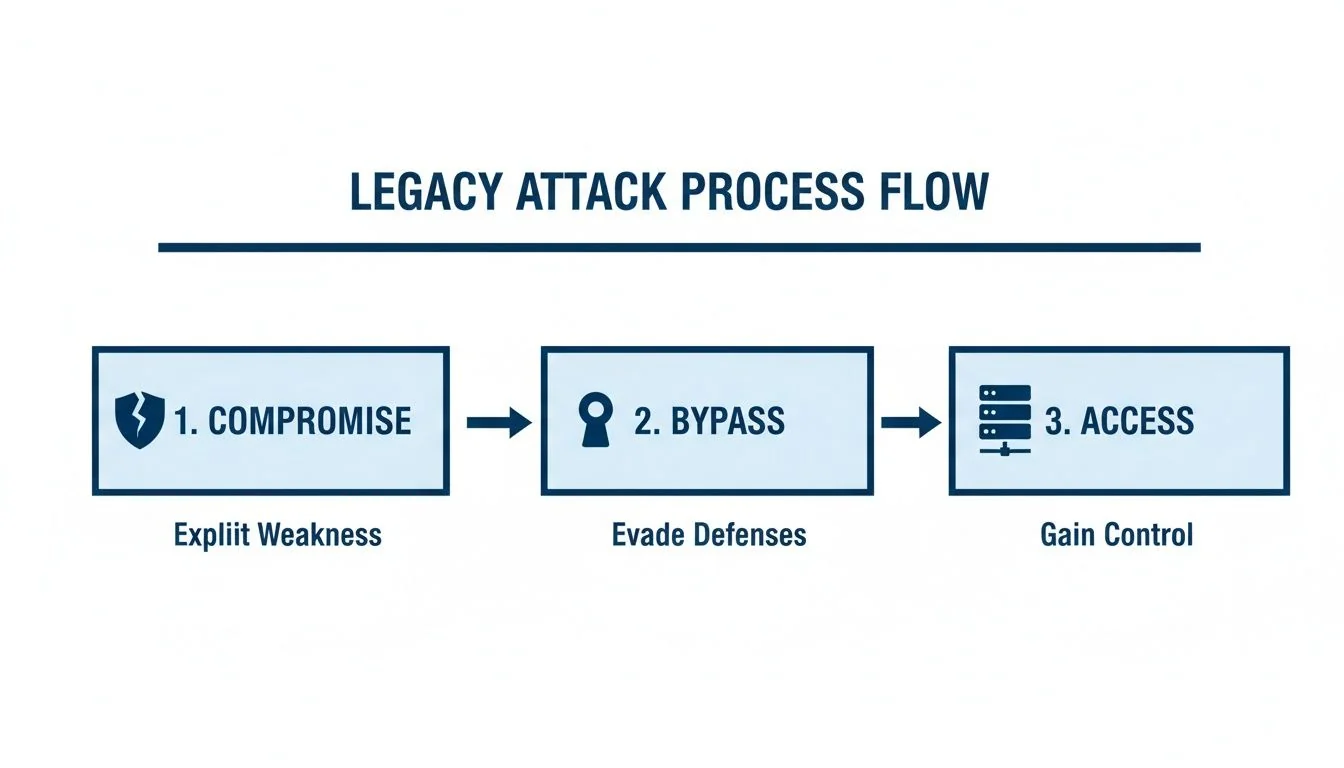
The initial compromise is the only hard part for an attacker. After that, protocols like NTLM and Basic Auth let them bypass the MFA and conditional access policies you have spent years building.
Phase 1: Audit and Isolate (First 90 Days)
You cannot fix what you cannot see. The first 90 days are about discovery and containment—mapping your entire authentication landscape and strangling the most dangerous legacy protocols to shrink the immediate attack surface. This requires deep traffic analysis to find every script, appliance, and application still using protocols like Basic Auth, Kerberos, or NTLM.
Your immediate action items:
- Log Analysis: Dig through your IdP, firewall, and VPN logs. Hunt for patterns like
BAV2ROPCor clients hitting IMAP/POP3 endpoints without modern auth headers. This is your evidence. - Dependency Mapping: Build a definitive inventory of applications and the authentication protocols they use. This map becomes the foundational document for the entire project.
- Containment: Get aggressive. Use conditional access policies and firewall rules to block legacy protocols wherever possible. If a critical app must use one, isolate it on a segmented network with intense monitoring.
Phase 2: Bridge and Abstract
With a clear map of your legacy dependencies, you now build a bridge to the future. Rewriting every app is not feasible, so you introduce an identity provider (IdP) or an authentication gateway that acts as a translation layer.
This layer’s job is to abstract the old protocols away from your applications. It speaks modern standards like OIDC and SAML to new services while still communicating with older systems in their native tongue (Kerberos, LDAP, etc.). This decoupling is the key that unlocks incremental migration.
This abstraction layer is the most critical component of a successful modernization. It allows you to move applications one by one, at your own pace, without being forced into an all-or-nothing cutover. It turns an impossible problem into a series of manageable, low-risk steps.
This is where your security identity modernization strategy moves from theory to practice. You can now methodically improve your security posture without breaking the business.
Phase 3: Deprecate and Enforce
With the bridge in place and apps moving over, the final phase is about turning off the old systems for good. This is a deliberate, methodical process of decommissioning legacy endpoints, servers, and protocols. This is also where you raise the security bar for the entire organization.
Key actions for this phase:
- Decommission Legacy Systems: As applications are migrated to the new IdP, you can finally power down old LDAP servers, Active Directory Federation Services (ADFS) instances, and other relics.
- Enforce Phishing-Resistant MFA: With a modern identity platform, you can mandate strong authenticators like FIDO2/WebAuthn or certificate-based auth. This moves the company beyond vulnerable methods like SMS and push notifications.
- Clean Up Service Accounts: This is the perfect opportunity to tackle the decades-old problem of static service account credentials. Migrate them to managed identities or a modern secrets management platform to eliminate hardcoded passwords.
This three-phase playbook transforms a daunting technical liability into a structured, achievable project. It provides a clear path to eliminating risk while building a resilient identity foundation.
How to Vet Your Modernization Partners
Picking the wrong partner for an identity migration is a career-limiting move. A botched migration leads to catastrophic downtime, security breaches, and project failures that burn through millions in budget. Your job is to find a partner who has navigated this specific minefield before—not one learning on your dime.
Forget the marketing slicks. You need to cut through the fluff with questions that reveal genuine, hard-won expertise. A partner who only talks about “best practices” is a red flag. A partner who can detail their last three emergency rollbacks is a contender.
Ditching Surface-Level Questions
Standard questions get rehearsed answers. Asking, “Do you have experience with legacy authentication?” is useless. You must probe for specific, technical depth that cannot be faked.
Your questions must be laser-focused on the ugliest, most complex parts of the job—the exact points where these migrations fail.
-
Bad Question: “Can you help us migrate from Active Directory?”
-
Good Question: “Describe a project where you decoupled a critical monolith from a central LDAP without downtime. What was your abstraction strategy, and how did you manage the cutover for service accounts?”
-
Bad Question: “Are you familiar with cloud identity providers?”
-
Good Question: “Show us your playbook for migrating hundreds of service accounts that rely on Kerberos delegation to a modern, OIDC-based architecture. How do you handle secrets rotation during the transition?”
These questions force a conversation about implementation specifics. An experienced partner will have detailed, opinionated answers. A weak one will stumble.
The Technical Depth Vetting Framework
Use this framework to structure your evaluation. The goal is to score potential partners on their proven ability to handle the messy reality of modernization, not just their sales pitch.
| Vetting Category | Key Questions to Ask | What a Strong Answer Looks Like | Red Flags |
|---|---|---|---|
| Dependency Management | How do you map and untangle tightly coupled dependencies on legacy protocols like Kerberos or NTLM? | They describe using traffic analysis tools, abstraction layers (proxies/gateways), and a phased approach to isolate and migrate apps individually. | They suggest a “big bang” cutover or focus only on rewriting applications, ignoring the underlying protocol dependencies. |
| Downtime Mitigation | Walk us through your strategy for a zero-downtime migration of a mission-critical, user-facing application. | They talk about blue-green deployments, feature flagging for authentication methods, and robust rollback plans tested in pre-production. | They are vague about cutover mechanics or claim “it’s a seamless process” without detailing how they ensure seamlessness. |
| Service Account Strategy | What is your process for discovering, cataloging, and migrating non-human identities and service accounts? | They present a multi-stage plan: discovery, risk assessment, migrating to managed identities or a vault, and enforcing least-privilege access. | They treat service accounts as an afterthought or suggest manually updating config files, signaling a lack of automation. |
| Failure Scenarios | Describe your most challenging identity migration failure. What went wrong, how did you recover, and what did you change in your process? | They provide a specific, technical post-mortem, take ownership of the mistake, and show how it led to a stronger, more resilient process. | They claim they’ve never had a major failure, blame the client or a third-party tool, or give a generic answer. |
A partner’s willingness to dissect their failures is the single greatest indicator of their expertise. Success stories are easy to invent; battle scars are earned. The partner you want is the one who can tell you exactly why a project went sideways and how they fixed it under pressure.
Choosing the right partner is the most important decision in this process. It is the difference between a successful modernization that secures your business and a costly failure that sets you back years. Use this evidence-based approach to ensure you are hiring a team that has already solved the problems you are about to face.
Next Steps: Building the Business Case
Spotting the technical flaws in a legacy authentication system is the easy part. The real work is convincing the business to fund the fix. You must translate technical liabilities into the language the board understands: financial risk, competitive edge, and strategic growth.
This is not another IT cost center. It is a strategic investment that slashes the odds of a multi-million-dollar breach, trims operational drag, and removes the single biggest blocker on your digital roadmap. The conversation must shift from, “How much will this cost?” to “What is the daily cost of doing nothing?”
Quantifying the Financial Upside
To get this funded, you must connect every technical fix to a hard number. Abstract security improvements do not get checks signed. A clear ROI does.
- Reduced Breach Probability: Frame this investment against the $2.5 million average cost of an identity-driven breach. Modernizing your auth stack cuts this risk by a measurable percentage.
- Lower Cyber Insurance Premiums: Insurers now dig into authentication protocols. Show how ripping out Basic Auth can lead to premium reductions of 20-50%—or prevent an outright denial of coverage.
- Accelerated Project Timelines: Legacy dependencies are an anchor. Quantify this “technical debt tax” by showing how much longer cloud migrations or new app deployments take because of endless authentication workarounds.
The urgency is underscored by data showing that in the first half of 2025 alone, ransomware attacks shot up by 179%, while credential theft exploded by 800%. Attackers are feasting on weaknesses in outdated MFA systems.
Worse, our own analysis at Modernization Intel of over 200 partners reveals that companies clinging to these old protocols see 67% higher failure rates in their cloud migrations, all because of tangled legacy auth dependencies. You can read the full research on these surging attack rates.
Your First 90 Days Execution Checklist
Once you get the green light, momentum is everything. This is a business execution plan designed to show immediate, tangible progress.
Your business case must answer one question for the executive team: “How does this investment make the business faster, safer, and more profitable?” Frame every metric, risk, and milestone around this objective.
-
Days 1-30: Discovery and Baseline
- Action: Deploy discovery tools and analyze logs to build a definitive inventory of every application still using legacy protocols.
- Deliverable: A risk-prioritized “hit list” of the top 10 most vulnerable applications. Pair this with a baseline of current operational costs, like the volume of helpdesk tickets for password resets.
-
Days 31-60: Pilot and Partner Selection
- Action: Pick a non-critical but representative application for a pilot migration. Simultaneously, vet modernization partners using the rigorous framework from the previous section.
- Deliverable: A successful pilot migration that proves the model works, and a signed contract with a partner who has passed your vetting.
-
Days 61-90: Isolate and Communicate
- Action: Begin rolling out containment policies. Block legacy auth for non-essential services to immediately shrink your attack surface.
- Deliverable: A report showing a measurable reduction in exposure and a clear, communicated roadmap for the next phase of the migration.
Frequently Asked Questions
What is the biggest mistake companies make with legacy authentication?
The biggest mistake is treating it as a low-priority technical problem, ignoring the massive business risk it represents. Legacy auth is not just an old system; it is an active liability.
It blocks cloud adoption, bloats project budgets with workarounds, and creates security backdoors that modern tools cannot see. By failing to translate legacy authentication system risks into dollars—breach costs, compliance fines, project delays—technical leaders never get the executive buy-in they need. It remains an underfunded IT task instead of a critical initiative to de-risk the entire business.
Is a full migration feasible for tightly coupled core applications?
Yes, but a “big bang” cutover is almost always the wrong approach. The successful strategy is a “bridge and abstract” model.
You introduce a modern identity provider to sit in front of the old one. It acts as a smart proxy, speaking legacy protocols like Kerberos to old applications while presenting modern interfaces like OIDC/SAML to the rest of your systems.
This approach decouples applications from the legacy system one by one, allowing for a phased, incremental migration without a high-risk, all-or-nothing cutover. It methodically shrinks your exposure to legacy authentication system risks without breaking critical business operations.
It transforms an impossibly large problem into a series of manageable, low-risk steps.
When does it make sense not to modernize an auth system?
Almost never. The only exception is a system that meets all of these criteria:
- It is completely air-gapped, with zero connectivity to any external network.
- It has a fixed, documented, and shrinking user base. No new users are being added.
- It is already formally scheduled for decommissioning within the next 6-12 months.
If you can prove that the cost of a bridging solution and migration effort is demonstrably higher than the quantifiable risk for its very short remaining lifespan, you can make a defensible business case to accept that risk. Even then, you would need compensating controls like constant monitoring. It is an extremely rare scenario.