A CTO's Guide to CICS Transaction Modernization Approaches
The decision is no longer if you should modernize CICS transactions, but how. Most teams get trapped debating three paths: Rehosting (lift and shift), API Wrapping (incremental strangulation), and Full Refactoring (cloud-native rewrite). Each represents a wildly different bet on speed, cost, risk, and future technical debt. Choosing the wrong path is the leading cause of the 67% failure rate for mainframe modernization projects.
Choosing Your CICS Modernization Path
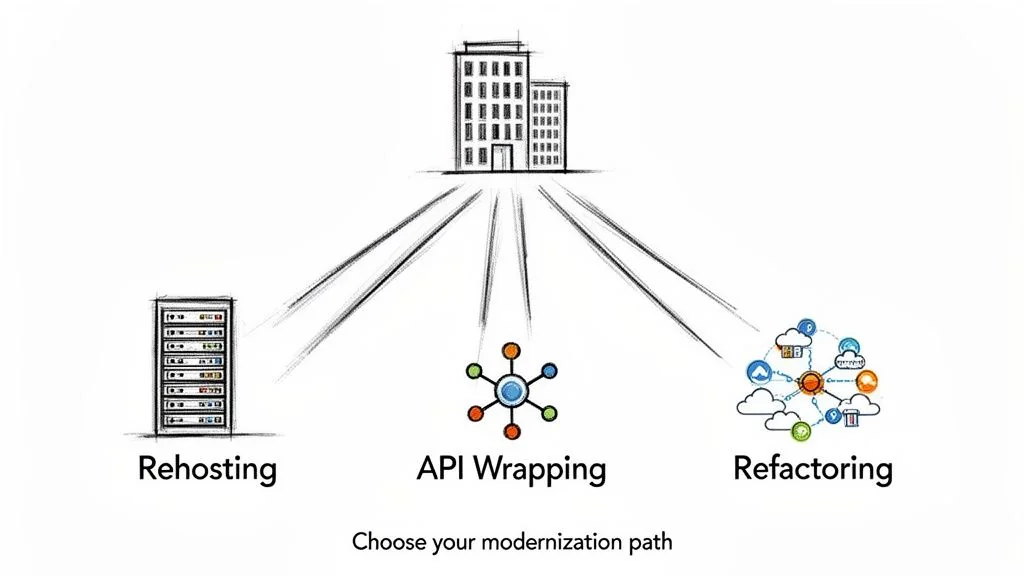
This choice defines your IT budget, operational stability, and ability to innovate for the next decade. Get it right, and you unlock agility and slash MIPS costs. Get it wrong, and you join the majority of failed projects plagued by data corruption, budget overruns, and catastrophic rollbacks. This guide moves past marketing fluff to provide a technical comparison of the three core strategies, based on post-mortems of over 50 CICS modernization initiatives. For a higher-level view, you can review this primer on how to modernize legacy applications.
CICS Modernization Approaches At a Glance
This table provides a high-level comparison. The real decision lies in the technical trade-offs detailed in subsequent sections.
| Approach | Primary Goal | Typical Timeline | Cost Profile | Risk Level |
|---|---|---|---|---|
| Rehosting | Rapidly exit the mainframe to reduce MIPS costs. | 6–12 months | Low (Upfront) | Low (Technical), High (Vendor Lock-in) |
| API Wrapping | Incrementally modernize and expose legacy logic. | 12–36 months | Medium (Phased) | Medium |
| Full Refactoring | Achieve cloud-native architecture and agility. | 24–48+ months | High (Capital Intensive) | High |
The “right” choice depends on your specific risk tolerance, budget, and business goals.
Evaluating Rehosting for CICS Workloads
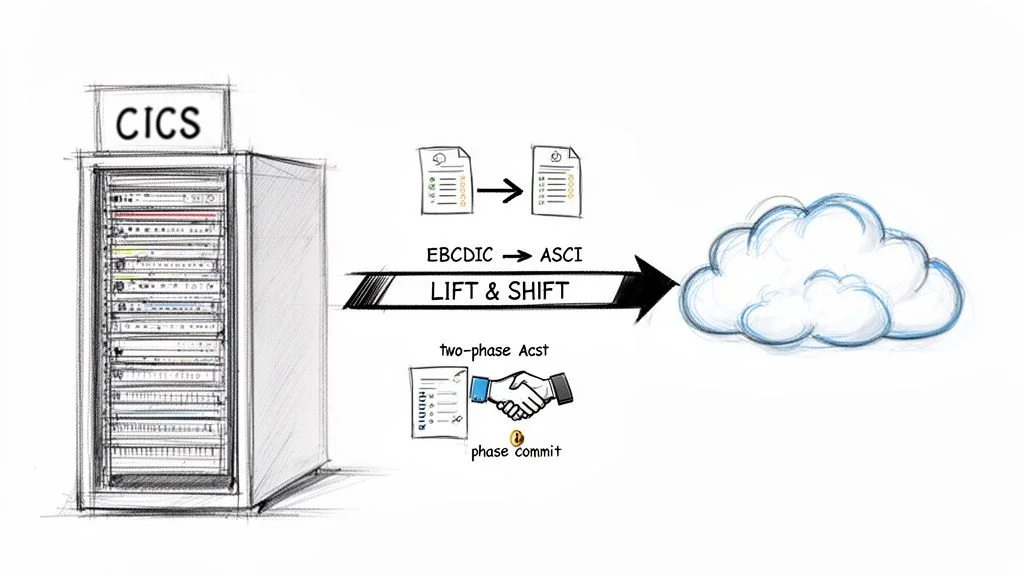
Rehosting, or “lift and shift,” is pitched as the fastest way off the mainframe. The strategy is to move COBOL applications and their dependencies (JCL, VSAM, Db2) to a cloud environment with minimal code changes. The value proposition is direct: stop paying for MIPS.
This is not a drag-and-drop operation. This approach leans entirely on specialized mainframe emulation software from vendors like Micro Focus or platforms like AWS Mainframe Modernization. These tools create a simulated z/OS environment on Linux, providing runtimes that interpret JCL, manage CICS transactions, and handle mainframe data formats. The upfront cost is compelling, typically $1.50 to $2.50 per line of code (LOC) for the migration project. But this is not the total cost. You are swapping mainframe licensing for emulation software licensing and cloud infrastructure costs.
Technical Hurdles in Rehosting
The appeal of rehosting is sidestepping a rewrite. The trade-off is that you are asking an emulation layer to perfectly replicate critical mainframe behaviors that have no native cloud equivalent. Failure comes down to how the platform handles three specific, high-risk constructs.
- Transactional Integrity (Two-Phase Commit): CICS guarantees a transaction involving multiple resources (Db2 table, VSAM file) either fully completes or fully rolls back via a built-in two-phase commit (2PC). If the emulation tool’s 2PC is not flawless, you risk partial commits that leave data in a corrupt, inconsistent state—a catastrophic failure for a financial system.
- State Management: CICS manages application state within its memory (e.g., COMMAREA). In a stateless cloud environment, this state must be externalized. This introduces latency and creates new points of failure that did not exist on the mainframe.
- Data Conversion (EBCDIC to ASCII): The real danger is not the character set conversion; it is in proprietary data formats like
COMP-3packed decimals. A single misstep in converting these numeric types will cause silent data corruption, where the system appears to work but produces fundamentally wrong calculations.
A common failure pattern we observe is an oversimplified approach to data migration. Teams focus on the character set conversion and overlook the precision risk in packed decimal fields. This results in systems that appear to function correctly but produce incorrect financial reports, a defect that often goes undiscovered until months after cutover.
When to Choose Rehosting
Rehosting is a valid tactic if your primary goal is exiting a mainframe hardware contract quickly and your CICS applications are stable, black-box systems. It is a pure infrastructure play.
It is the wrong choice if you plan to evolve the application’s business logic. You are not eliminating technical debt; you are moving it to a more complex environment. You escape hardware vendor lock-in only to create a new dependency on a niche emulation software vendor, and your need for COBOL developers does not go away.
Strangling CICS with API Wrapping
API wrapping, combined with the Strangler Fig pattern, is the go-to incremental play for modernizing CICS transactions. Instead of a high-risk “big bang” rewrite, you build a new application that slowly encircles the mainframe. This involves wrapping legacy CICS transactions with modern REST or GraphQL APIs, creating a facade that hides the COBOL and BMS maps underneath.
This approach gives you a lever to incrementally kill off legacy logic. Initially, new APIs pass requests to the mainframe. Over time, you can redirect traffic for specific functions to new microservices that first replicate, then improve upon the original business logic. You starve the mainframe of its purpose, one transaction at a time.
The Anti-Corruption Layer: Your Architectural Firewall
The entire strategy lives or dies by the quality of your anti-corruption layer (ACL). The ACL’s job is to mediate between your clean microservices and the messy, stateful reality of the mainframe. Its primary role is translating modern JSON payloads into the fixed-length formats COBOL copybooks expect and handling EBCDIC to ASCII conversions.
A battle-hardened ACL handles three non-negotiable functions:
- Protocol Translation: It must convert HTTP/REST calls into something CICS understands, typically via the CICS Transaction Gateway (CTG) or z/OS Connect.
- Data Transformation: The ACL maps flexible JSON to and from rigid COBOL copybooks. A single mismatched data type or length can bring a transaction crashing down.
- State Management: It must mimic mainframe statefulness in a stateless world, typically using a distributed cache to manage session data that would normally live in CICS memory.
Think of the ACL as your defense against letting mainframe constraints leak into your modern architecture. If you get this wrong, your new microservices become a distributed monolith with extra network hops.
A telecom giant we worked with used this pattern to modernize its core billing system. By wrapping critical CICS transactions, they launched a new customer self-service portal. Initially, 100% of requests passed to the mainframe. Within 18 months, they had rerouted 60% of the transaction logic to new microservices, boosting transaction throughput by 180% without a minute of planned downtime.
Where These Projects Fail (And How to Avoid It)
API wrapping has predictable failure modes. The number one killer is performance. Every API call adds latency—the request traverses your gateway, the ACL, and multiple network hops before it hits the mainframe. Without obsessive performance engineering, this latency kills the user experience.
The second most common failure is data consistency. During the transition, data exists in two places: the legacy Db2/VSAM files and the new databases for your microservices. Maintaining transactional integrity is a nightmare. Teams often discover they need distributed transaction patterns like Sagas but underestimate the complexity.
To keep your project from becoming another statistic:
- Cache Aggressively: Implement a distributed cache inside the ACL to hold frequently accessed, non-volatile data. Every round trip you can avoid is a win.
- Be Brutal with Payloads: The ACL must request only the specific data fields needed. Pulling entire records “just in case” is a classic performance anti-pattern.
- Design for Dual-Writes from Day One: Don’t treat data synchronization as a future problem. You need a robust data sync strategy from the start, whether it’s an event-driven architecture with Kafka or a managed dual-write protocol with reconciliation jobs. You must have a clear plan for when the new system becomes the single source of truth.
This is a pragmatic middle ground. It delivers visible value incrementally while keeping risk in check. Costs are typically milestone-based, spreading your investment.
Going All-In: A Full Refactoring to Cloud-Native
Full refactoring is not a modernization step; it is a declaration of strategic intent. You rebuild the CICS application from the ground up as a cloud-native system in a language like Java or C#. This is the most aggressive and expensive path, aimed at eliminating technical debt for good.
The business case is not short-term cost savings. It is about unlocking future value and agility that the mainframe cannot provide. The goal is a microservices-based application where components can be developed, deployed, and scaled independently. The upfront investment reflects this ambition, typically running $2.50 to over $5.00 per LOC. This is a high-risk, high-reward bet. When it works, the results are dramatic. A federal agency we audited refactored its CICS-based claims processing system; transaction failures plummeted from 1.2% to 0.03%.
Technical Complexities and Common Failure Points
These projects fail from a gross underestimation of the work required to untangle and preserve decades of business logic baked into monolithic COBOL.
-
Business Rule Extraction: This is the most treacherous step. Automated tools can help identify logic paths, but they cannot interpret the intent behind convoluted code riddled with high cyclomatic complexity and
GO TOstatements. Without meticulous human oversight, you will miss critical business functions. -
Data Modernization: Moving from VSAM or Db2 to a cloud database like PostgreSQL or DynamoDB is fraught with peril. The main challenges are ensuring absolute data integrity. Incorrectly mapping a mainframe data type like
COMP-3can lead to silent data corruption that poisons your system for months before detection. -
State and Transaction Management: CICS provides transactional integrity (ACID properties) out of the box. In a distributed microservices architecture, you must build this yourself. This means implementing complex patterns like Sagas, which are notoriously difficult to get right and can easily introduce data consistency problems.
The market for mainframe data services is set to hit $15 billion by 2025, with cloud-native refactoring being a stated goal for 80% of enterprises. Yet, our post-mortems of over 50 CICS modernization projects show a staggering 67% failure rate directly caused by data governance mistakes. You can discover more insights about how AI-driven automation helps solve these challenges.
When to Commit to Full Refactoring
Despite the risks, refactoring is the only approach that genuinely future-proofs a core business application. It becomes the right move when your business can no longer afford the constraints imposed by the mainframe.
Full refactoring is a bet on the future value of agility. Choose this path only when the cost of not changing—the inability to launch new products, integrate with partners, or attract modern engineering talent—becomes greater than the risk of the rewrite itself.
This all-or-nothing approach is necessary when:
- Business logic requires constant, rapid evolution, and the COBOL deployment cycle is a critical business bottleneck.
- The application must integrate deeply with a modern, cloud-native ecosystem of APIs and services.
- You have a strategic mandate to exit the mainframe entirely, including its licensing and shrinking talent pool. For a deeper look at moving complex workloads to scalable platforms, read our guide on migrating applications to Kubernetes.
Avoid a full refactoring if your primary driver is quick cost reduction or if the application’s business logic is stable. The immense risk and expense almost never justify the outcome in those scenarios.
A Decision Matrix for CICS Modernization
Choosing the right CICS modernization strategy is a high-leverage decision, yet 67% of projects fail. This happens when teams make a gut call instead of running a structured evaluation. A choice made without evidence is a guess, and a bad guess here can set your business back years. Success demands a rigorous, evidence-based approach based on data-driven decision making.
CICS Modernization Technical Decision Matrix
This matrix is designed to force the hard conversations, mapping the technical realities of each approach to your specific goals. Cost and risk assessments are based on real project data.
| Evaluation Criterion | Rehosting | API Wrapping (Strangler) | Full Refactoring |
|---|---|---|---|
| Transactional Integrity | ACID (High Risk): Relies on the emulator’s 2PC fidelity. This is a black box. If it’s imperfect, you get silent data corruption. | ACID to BASE (Med Risk): Dual-write strategies are complex. Introduces eventual consistency challenges that mainframe teams are often unprepared for. | BASE (Low Risk): Designed for distributed systems from the ground up. Requires implementing Sagas or similar patterns, but the risk is understood and manageable. |
| State Management | High Latency: The emulator fakes COMMAREA and TSQs by externalizing state, which adds costly network hops to every interaction. | Medium Latency: State is managed in an Anti-Corruption Layer (ACL) cache. It’s complex to build but gives you control. | Low Latency: Natively stateless. State is handled explicitly per microservice or in a proper distributed cache like Redis. |
| Data Format Handling | High Risk: EBCDIC and COMP-3 conversion is handled by the emulation software. You’re trusting a black box with no guarantee of precision. | Medium Risk: Handled within the ACL. The transformation logic must be explicitly written and tested, making it auditable but a development burden. | Low Risk: Natively modern data types. It’s a one-time, validated conversion during the migration, eliminating ongoing risk. |
| Upfront Cost (per LOC) | $1.50 - $2.50 | $0.50 - $1.50 (Initial API) | $2.50 - $5.00+ |
| Ongoing OpEx | Medium: You swap MIPS for expensive emulation software licenses and cloud infrastructure costs. It’s often just shifting the cost, not reducing it. | High (Initially): You are running two systems in parallel. Costs only decrease as the mainframe is strangled, which can take years. | Low: Optimized for cloud-native spending. Eliminates mainframe MIPS and proprietary emulation licensing entirely. |
With CICS underpinning 85% of core systems in Banking and Insurance and transaction volumes still growing 25% year-over-year, the pressure to modernize is immense. You can see more on the growing mainframe modernization market for context.
Matching the Approach to Your Risk Appetite
Your organization’s tolerance for risk is the most important variable. A strategy that works for a high-growth startup will bankrupt a risk-averse bank. The flowchart below maps risk appetite directly to a defensible modernization strategy.
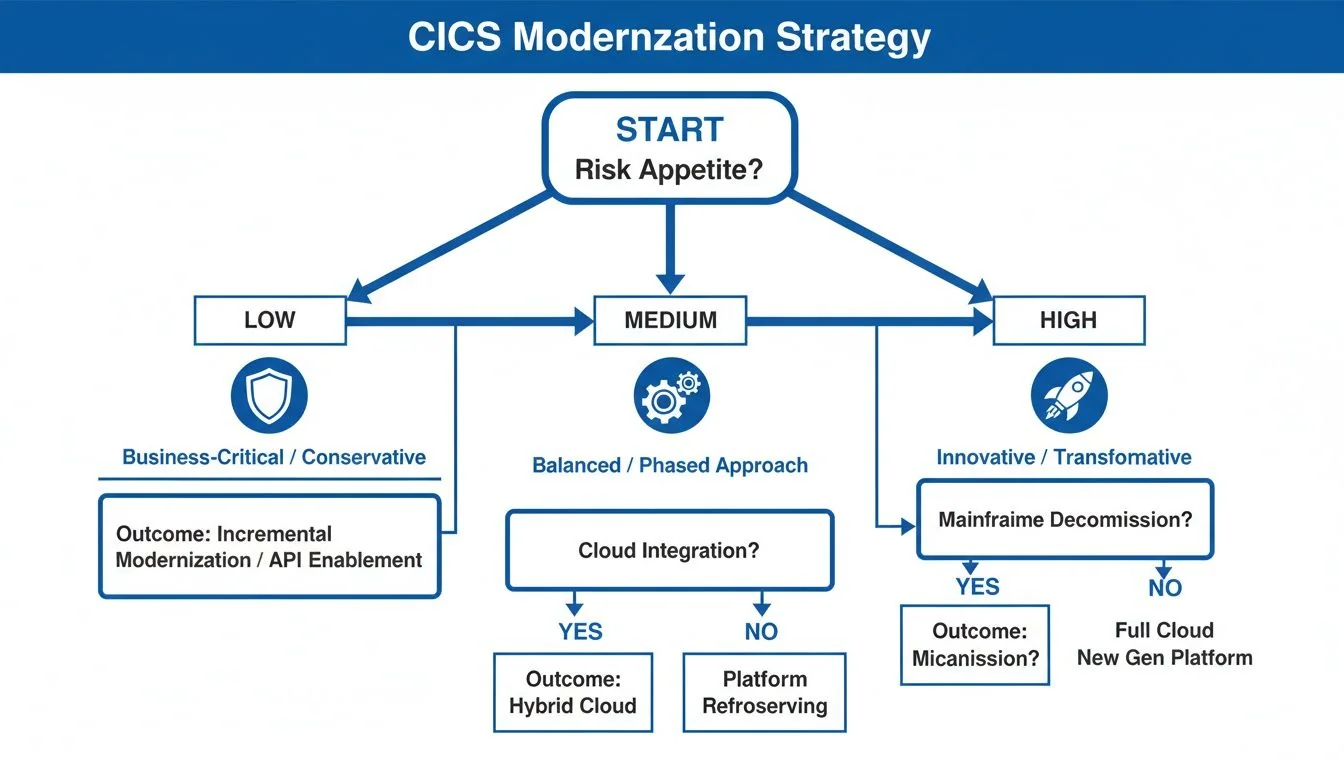
A low-risk organization will gravitate toward Rehosting for its speed. A high-risk, high-reward culture is the only one who should consider the payoff of a Full Refactoring.
The most common mistake we see is a mismatch between a company’s risk profile and its chosen strategy. A risk-averse organization attempting a “big bang” refactoring is setting itself up for failure. Likewise, a fast-moving digital company would be crippled by a rehosting project that just preserves decades of technical debt.
Using a structured framework forces an honest conversation about your team’s real capabilities, budget, and strategic goals. It leads to a choice that is not only technically sound but, more importantly, organizationally survivable.
Next Steps: De-Risking Your Modernization Project
A pilot project is where your strategy meets reality, and it’s the single biggest predictor of whether your CICS modernization program succeeds or joins the 70% that fail. A poorly scoped pilot—either a trivial “hello world” transaction that proves nothing or a multi-system behemoth that’s doomed from the start—is a common failure. The goal is to find the sweet spot: a transaction with enough business impact to matter and enough technical complexity to be a meaningful test.
How to Select a Pilot That Won’t Get You Fired
Your ideal pilot is not a single, isolated program. Target a small cluster of 3-5 related transactions. This forces you to confront real-world challenges like inter-program calls and shared data access immediately. Use this checklist to score your candidates.
- Business Impact: Does this transaction cluster support a critical business process? A win here gets executive buy-in.
- Technical Isolation: How many other systems does it talk to? The fewer the external dependencies, the better. You want to contain the blast radius.
- Data Complexity: Does it touch both Db2 and VSAM? Good. You want to force a showdown with your data access strategy early.
- Performance Baseline: Do you have hard, reliable performance numbers for these transactions? You cannot declare victory if you do not know the starting line.
Vetting Partners: Separating Specialists from Generalists
Your average cloud migration partner will fail. They will stumble over COMP-3 packed decimal fields, EBCDIC-to-ASCII data corruption, and the loss of CICS’s two-phase commit. You need a specialist who has the scars to prove they have done this before.
Don’t ask, “Have you done a CICS modernization before?” Ask, “Describe the last time a
COMP-3data corruption issue blew up a data feed post-migration and exactly how your team fixed it.” The first question gets a sales deck. The second gets the truth about their experience.
Drill down with these questions in your RFP:
- Describe your methodology for extracting and validating business rules from a 50,000-line COBOL program with high cyclomatic complexity. (This exposes their process for tackling the single riskiest part of any refactoring).
- How do you guarantee transactional integrity when replacing a CICS two-phase commit with distributed sagas? (This tests their understanding of ACID guarantees versus eventual consistency).
- Provide a sanitized case study where you managed a dual-write data consistency strategy for a Strangler Fig implementation. Show us the reconciliation reports. (This proves they’ve navigated the hell of running old and new systems in parallel).
Picking the right pilot and partner moves your CICS modernization from a theoretical plan to a de-risked, measurable project. It’s the first, and most important, step.
Frequently Asked Questions About CICS Modernization
Once the high-level strategy is set, CTOs ask the questions that determine project success. Below are blunt answers to common technical and strategic concerns.
What Happens to CICS Transactional Integrity?
CICS’s guarantee of transactional integrity via its built-in two-phase commit (2PC) is the gold standard. Each modernization path compromises this guarantee differently.
- Rehosting: You place 100% faith in the emulator’s 2PC fidelity. If that emulation software has a bug, you risk silent data corruption. This is a black-box risk.
- API Wrapping: The responsibility for integrity shifts to you. While strangling the monolith, you run two systems in parallel. This forces you into eventual consistency, requiring complex data synchronization patterns and adding significant operational overhead.
- Full Refactoring: You explicitly trade ACID for BASE (Basically Available, Soft state, Eventually consistent). You architect for it yourself using patterns like Sagas. The logic is open and auditable, not hidden inside a vendor’s black box.
Can We Finally Get Rid of Our COBOL Developers?
This question comes up in every kickoff meeting. The answer almost always disappoints someone.
A common—and expensive—misconception is that any modernization project immediately solves the mainframe talent problem. In reality, only the most difficult and costly path actually achieves this.
- Rehosting and API Wrapping absolutely do not eliminate your need for COBOL developers. With rehosting, you run the same COBOL code. For API wrapping, your COBOL core remains the system of record for years, demanding maintenance.
- Full Refactoring is the only approach that removes the COBOL dependency. By rewriting the application in a modern language like Java or C#, you finally cut the cord.
What Is the Realistic Impact on Performance?
Performance will almost certainly get worse before it gets better. Moving transactions off hyper-optimized, co-located mainframe hardware introduces network latency.
For rehosting, every emulated CICS feature—like passing data via COMMAREA—morphs from an in-memory operation into a network call, adding latency. With API wrapping, the anti-corruption layer adds another network hop.
Successful projects plan for this initial degradation. They aggressively redesign chatty interactions and implement caching strategies from day one, clawing back performance piece by piece.